Herbert Lin, a cybersecurity researcher at Stanford University and former hacker, still carries around his physics textbooks from 40 years ago
By Katherine Kornei
Herbert Lin spends most of his time thinking about cybersecurity, data breaches, and power grids, all from a physics perspective. Lin, a senior research scholar and Hank J. Holland Fellow in Cyber Policy and Security at Stanford University, acknowledges he hasn’t used graduate-level physics since his qualifying exam in the 1970s. "But it still affects everything about the way that I look at the world," he says. Lin even carries around his 40-year-old physics textbooks whenever he moves. "I should get rid of those books," he says. "But I can’t. It’s like cutting off an arm."
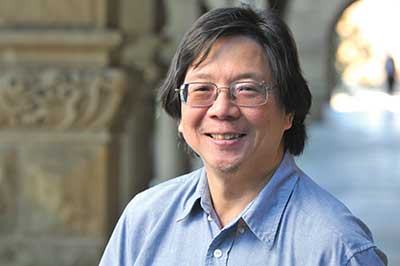
Herbert Lin
The physicist at heart is also fascinated by psychology and sociology. Lin’s doctoral research at MIT focused on the psychological difficulties that undergraduates encounter when learning physics. "I wanted to understand better what it meant to be a good teacher," he says. There are definite differences in how physicists and social scientists tackle a challenge, however, Lin notes. "[Physics is about] stripping a problem down to its essence," he says. "That method drives social scientists crazy—they like to consider a problem in all of its complexity."
Physics, psychology, economics, and sociology collide at the intersection of public policy and cybersecurity, where Lin has been working in some form for the last 25 years. Lin’s interest in cyber-security developed in high school. "I was able to explore computer security, shall we say … and I never abandoned the mindset of a hacker," he says. These days, Lin spends his time thinking about how to attribute breaches in cybersecurity, international diplomacy ("I think a lot about North Korea," he says), and what is an appropriate response to a cyber attack. "Mostly we think about how people are hacking us," he says. "But maybe we might want to hack them."
Lin is also an amateur magician, and he’s quick to note the parallels between sleight of hand and his day job. In both magic and cybersecurity, you have to "pre-implant vulnerabilities," he said at a Stanford University seminar in 2015. With a magic trick, creating a vulnerability might be as simple as hiding a particular card under a participant’s seat in advance, Lin says. In the field of cybersecurity, ensuring a vulnerability might involve designing a missile that turns off when it receives a certain radar code, for example. "You have to set the stage so when you come into it later on you can take advantage of what’s there," Lin said at the seminar.
The Equifax data breach in September 2017—in which information from 143 million consumers was stolen from the credit reporting agency—is one recent example of a cybersecurity incident that affected the public. In an op-ed piece in the Washington Post, Lin advocated one way of combating similar events in the future: "Individual [credit] reports [should] be frozen by default, "thaw-able" only with the individual’s consent," he wrote. Such a requirement, if enforced technically, would help to ensure that the sensitive data contained within the reports were available to others only with the permission of the individual associated with that credit report. But this idea isn’t likely to make it into policy anytime soon, Lin concedes, because selling credit reports is big business: Equifax’s 2016 revenue topped $3 billion, Lin noted in his op-ed.
Data breaches aren’t going away anytime soon, Lin says. "Every boardroom should be contemplating the possibility that its company’s computer systems will be destroyed and private email, salary information, and much more publicly revealed," Lin wrote in 2015.
Given his front-row seat to the limitations of technology, Lin has some reservations about the burgeoning "Internet of things," the growing system of networked devices that share data over the Internet. He recounted an incident a few years ago with an Internet-enabled thermostat, which was programmed by a smartphone. "It crashed in such a way that you couldn’t turn on the heat, and there were people who froze," he says. "That is just totally asinine."
"I’ll be damned," Lin says, "if I’m going to put in an Internet refrigerator."
The author is a freelance writer based in Portland, Oregon.
©1995 - 2024, AMERICAN PHYSICAL SOCIETY
APS encourages the redistribution of the materials included in this newspaper provided that attribution to the source is noted and the materials are not truncated or changed.
Editor: David Voss
Contributing Correspondent: Alaina G. Levine
Publication Designer and Production: Nancy Bennett-Karasik
March 2018 (Volume 27, Number 3)
Articles in this Issue

